Table of Contents
Overview of NIST Cybersecurity Framework 2.0
We previously published a detailed article on NIST CSF 2.0. However, it’s crucial to understand this framework before we explore how IAM fits in.
The NIST Cybersecurity Framework (CSF) is a voluntary framework developed by the National Institute of Standards and Technology (NIST) that provides organizations with guidelines and best practices for managing cybersecurity risks. First released in 2014, version 2.0 of the CSF was released in February 2024 with updates that aim to make the framework more comprehensive and accessible.
The key goals and principles of CSF 2.0 include:
- Making the framework applicable to a broader range of organizations, not just critical infrastructure sectors
- Integrating privacy risk management practices
- Enhancing guidance for supply chain risk management
- Providing guidance on using cybersecurity frameworks for self-assessment
- Clarifying the relationship between CSF and other cybersecurity frameworks and standards
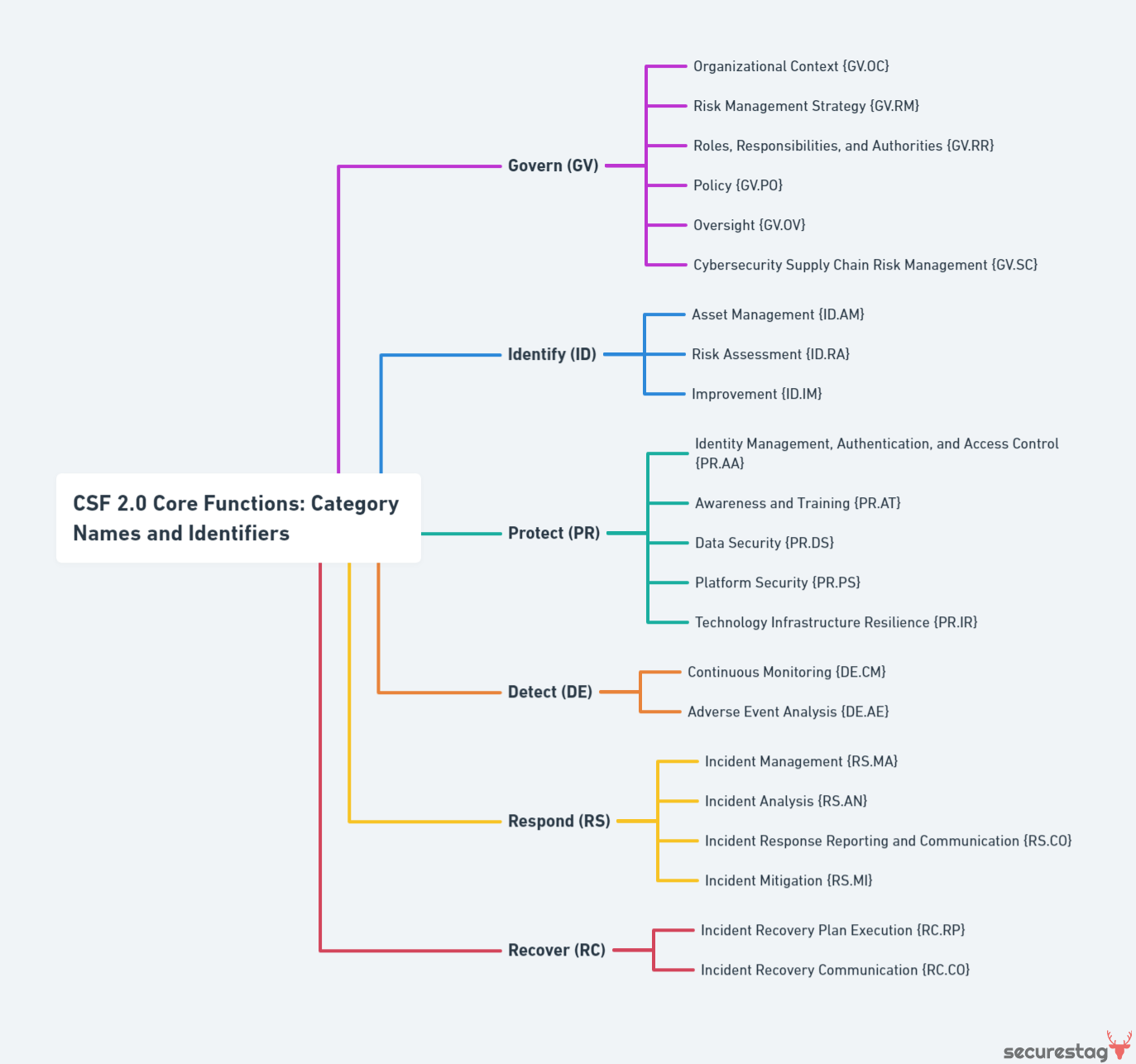
The CSF is structured around six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions provide a high-level view of the lifecycle of cybersecurity risk management.
- Govern – Develop and communicate the organization’s cybersecurity risk management policies and strategy
- Identify – Develop organizational understanding to manage cybersecurity risk
- Protect – Implement safeguards to ensure the delivery of critical services
- Detect – Develop and implement appropriate detection activities
- Respond – Take action regarding detected cybersecurity incidents
- Recover – Maintain resilience and restore capabilities after an incident
The CSF allows organizations to implement these functions and manage cybersecurity programs in a way that best suits their individual risk profile and needs.
Introduction to CSF 2.0: What’s New and Different
The National Institute of Standards and Technology (NIST) released version 2.0 of its Cybersecurity Framework (CSF) in February 2024. This updates the original 1.1 version published in 2018. CSF provides guidance on managing cybersecurity risk for organizations.
The 2.0 version introduces several significant changes and new features:
- The Core Functions have expanded from 5 to 6, with the addition of “Recover.” This brings a more significant focus on resilience and business continuity.
- “Govern” is a new Global element that guides how organizations can establish and communicate cybersecurity priorities.
- There is greater alignment with international standards like ISO and COBIT to enable easier integration.
- The 2.0 framework incorporates feedback from industry stakeholders and users of the original framework. There are clarifications and enhanced graphics for better usability.
- Subcategories across the core functions have been updated to reflect modern cybersecurity practices. For example, identity and access management are emphasized.
- Informative references now include guidance for small businesses and educational institutions.
The overarching benefit of CSF 2.0 is that it provides organizations with an up-to-date approach to managing cyber risks. The additional guidance and alignment with leading standards allow for easier implementation tailored to an organization’s needs. It enables businesses to be more cyber resilient and quickly respond to and recover from threats. With its flexible approach, CSF 2.0 can be a valuable resource for organizations of all types and sizes.
The Role of IAM in Cybersecurity
Identity and Access Management (IAM) refers to the policies, processes, and technologies used to control access to applications, systems, and data within an organization. IAM solutions aim to provide appropriate access levels while protecting sensitive information from unauthorized access.
IAM enhances an organization’s security posture in several key ways:
- IAM centralizes access control, enabling consistent policy enforcement across applications and systems. This reduces the risk of improper access due to human error or oversight.
- IAM implements the principle of least privilege, restricting users to only the access they require to perform their jobs. This limits damage from compromised accounts or insider threats.
- Multi-factor authentication and single sign-on capabilities provided by IAM make it more difficult for attackers to gain access by stealing credentials.
- Activity monitoring and access reviews enabled by IAM solutions improve visibility into access patterns and help identify inappropriate or unusual activity.
The main benefits of implementing a robust IAM program include:
- Increased organizational security through reduced vulnerability to cyber threats, such as data breaches, malware, and phishing.
- Improved compliance with regulations like HIPAA and PCI DSS by controlling access to sensitive data.
- Enhanced user productivity since users only have to remember one set of credentials.
- Reduced IT costs by consolidating redundant authentication systems.
In summary, IAM is critical in improving cybersecurity by restricting access, enforcing least privilege principles, and providing visibility into access patterns across an organization’s systems and applications.
Understanding IAM in CSF 2.0 Context
Identity and Access Management (IAM) plays a critical role in enhancing cybersecurity within the framework of CSF 2.0. By managing user identities and controlling access to systems and data, IAM directly supports several key functions outlined in CSF 2.0.
Specifically, IAM capabilities such as access governance, identity proofing, and privileged access management can help organizations to “develop and implement appropriate safeguards to ensure delivery of critical services” as part of the Identify function. These IAM controls also support the Protect function by limiting access and preventing unauthorized usage of systems and data.
Furthermore, IAM solutions’ auditing and monitoring features feed into the Detect function by providing visibility into authentication events and user activities. Finally, IAM facilitates the Response and Recovery functions by ensuring quick disablement of compromised accounts while minimizing disruption to unaffected users.
Implementing a robust IAM program with capabilities mapped to CSF 2.0 functions will strengthen cybersecurity posture across the board. IAM provides:
- An integrated, proactive approach to managing identities and access.
- Enhancing detection.
- Streamlining response.
- Enabling organizations to securely maintain business continuity.
Aligning IAM with the Identify Function
The Identify function outlines the need to develop an organizational understanding to manage cybersecurity risk. IAM strategies play a key role in enhancing this function.
Asset Management with IAM
Effective IAM allows organizations to identify what assets need protection through identity and access management. IAM systems provide visibility into which users have access to critical assets, enabling better asset management. According to CSF.tools, “Policies and procedures are established for permissible storage and access of identities used for authentication to ensure identities are only accessible based on rules of least privilege and replication limitation only to users explicitly defined as business necessary.”
Identity and Access Provisioning
IAM supports identity and access provisioning, ensuring identities are appropriately vetted, and appropriate access is granted based on roles and responsibilities. As CSF.tools states, “Account credential lifecycle management from instantiation through revocation, role-based access control (RBAC), and privilege management are maintained.”
Authentication Enhancements
Implementing robust authentication mechanisms is a key part of the Identify function. IAM provides capabilities like single sign-on (SSO) and multi-factor authentication (MFA) to ensure strong user authentication. According to NIST, the Identify function involves “establishing and understanding trust relationships between identities and credentials associated with assets, systems, networks or products.” IAM directly enables this.
IAM’s Impact on Protect and Detect Functions
Identity and Access Management strategies significantly enhance an organization’s ability to Protect critical assets and Detect cybersecurity events, as described in the NIST CSF.
The Protect function focuses on safeguarding assets and data through controls like access management, awareness training, and data security. IAM strengthens Protect capabilities by implementing strong authentication and authorization policies to limit access to authorized users. Segmentation and access controls based on the principle of least privilege ensure users only have access to the systems and data necessary for their roles. Data encryption also provides an additional layer of protection for sensitive assets.
For Detect, IAM improves visibility into user behavior through analytics and privileged access management. Monitoring anomalous activity is enhanced when normal baselines for user access are established through IAM controls. Limiting and closely governing privileged access facilitates auditing of admin actions. Integrated identity analytics provide further insights into potential threats.
IAM capabilities reinforce the Protect and Detect functions critical to cyber resilience by strengthening access policies, monitoring user activity, and securing data. Organizations implementing the NIST CSF can leverage IAM as an integral component of their overall security strategy.
Enhancing Response and Recovery with IAM
Identity and Access Management (IAM) plays a critical role in incident response and recovery by enabling organizations to quickly contain impacts, investigate breaches, and automate response workflows.
IAM solutions like single sign-on, access governance, and privileged access management can significantly improve an organization’s ability to respond to and recover from cyber incidents. For example, quickly disabling access or revoking compromised credentials during an incident can limit further damage. PR.IP-10 states that response and recovery plans should be regularly tested, and IAM capabilities directly support this.
Additional IAM capabilities like access certification, policy-based access controls, and automated provisioning/de-provisioning enable organizations to better understand and manage access. This improves visibility into which users have access to what resources, making it easier to investigate incidents and determine where the breach occurred.
By integrating IAM strategies into the NIST CSF framework, organizations can significantly enhance their ability to respond to incidents. Automating response workflows with IAM ensures rapid containment while access visibility and governance facilitate faster investigation and recovery. Overall, effective IAM implementation is critical to building cyber resiliency.
Best Practices for Implementing IAM with CSF 2.0
Implementing an effective IAM program within the NIST CSF 2.0 framework requires careful planning and execution. Here are some best practices to consider:
Strategies for Effective Integration
- Conduct a thorough review of existing identities, credentials, and access privileges to establish a baseline for improvement. This will illuminate areas of excessive permissions and potential vulnerabilities.
- Establish clear policies and procedures for granting least privilege access, onboarding/offboarding, and auditing user entitlements. Document these policies and train staff.
- To enhance identity assurance, implement multi-factor authentication for sensitive systems and data. Consider risk-based or adaptive authentication as well.
- Automate IAM processes like provisioning/de-provisioning and access reviews to improve efficiency and reduce human error.
Common Challenges and Solutions in IAM Implementation
- Lack of holistic visibility into identities and access. A centralized identity repository and entitlement reporting can mitigate this.
- Difficulty modeling and enforcing granular access controls. Attribute-based access control and dynamic authorization policies can help.
- Resource limitations for implementing IAM tools and training staff. Prioritize high-risk users and systems first. Seek incremental improvements.
- General organizational resistance to changing processes. Engage stakeholders early and highlight the benefits of improved security.
Organizational Adoption of IAM Best Practices
- Gain executive buy-in by connecting IAM to business risks, compliance, and overall cybersecurity posture.
- Involve IT teams, security leaders, and business unit managers in developing IAM roadmaps and policies.
- Provide training and support to help employees understand the importance of least privilege and data protection.
- Continuously monitor access and entitlements to identify anomalies and opportunities for tightening controls. This maintains visibility and ensures improvements over time.
Future of IAM in Cyber Frameworks
The threat landscape continuously evolves as new technologies emerge and attackers become more sophisticated. As such, the role of IAM in cybersecurity frameworks will need to adapt and expand. Here are some key trends shaping the future of IAM:
- Evolving threat landscape – As threats like ransomware, phishing, insider threats, and nation-state attacks become more complex, IAM will also need to evolve. IAM systems will require increased intelligence to detect anomalous behavior and customize access. Machine learning and AI will enable IAM to stay ahead of new threats.
- Emerging IAM capabilities – IAM systems are moving beyond simple access control to smart capabilities like risk-based authentication, automated user provisioning/de-provisioning, and privileged access management. As threats get smarter, IAM capabilities will become more adaptive, contextual, and seamless.
- Expanding the role of IAM in frameworks – As frameworks evolve, IAM’s role will expand from identity management to a strategic function across security, compliance, risk management, and user experience. IAM will move beyond IT into every facet of digital transformation. Frameworks will leverage IAM for greater visibility, automation, and orchestration across the cybersecurity stack.
The future of cybersecurity will be defined by intelligent, contextual IAM. As threats and technology evolve, IAM’s role in frameworks like NIST CSF will grow beyond access management into an essential capability for managing cyber risk. Organizations that strategically invest in IAM will gain a significant security advantage.